Broadwell case underscores broad scope of US email investigations
The FBI started its case in June with a collection of five e-mails, a few hundred kilobytes of data at most.
By the time the probe exploded into public view earlier this month, the FBI was sitting on a mountain of data containing the private communications — and intimate secrets — of a CIA director and a U.S. war commander. What the bureau didn't have — and apparently still doesn't — is evidence of a crime.
How that happened and what it means for privacy and national security are questions that have induced shudders in Washington and a queasy new understanding of the FBI's comprehensive access to the digital trails left by even top officials.
FBI and Justice Department officials have vigorously defended their handling of the case. "What we did was conduct the investigation the way we normally conduct a criminal investigation," Attorney General Eric Holder Jr. said Thursday. "We follow the facts."
But in this case, the trail cut across a seemingly vast territory with no clear indication of the boundaries, if any, that the FBI imposed on itself. The thrust of the investigation changed direction repeatedly and expanded dramatically in scope.
A criminal inquiry into e-mail harassment morphed into a national security probe of whether CIA Director David Petraeus and the secrets he guarded were at risk. After uncovering an extramarital affair, investigators shifted to the question of whether Petraeus was guilty of a security breach.
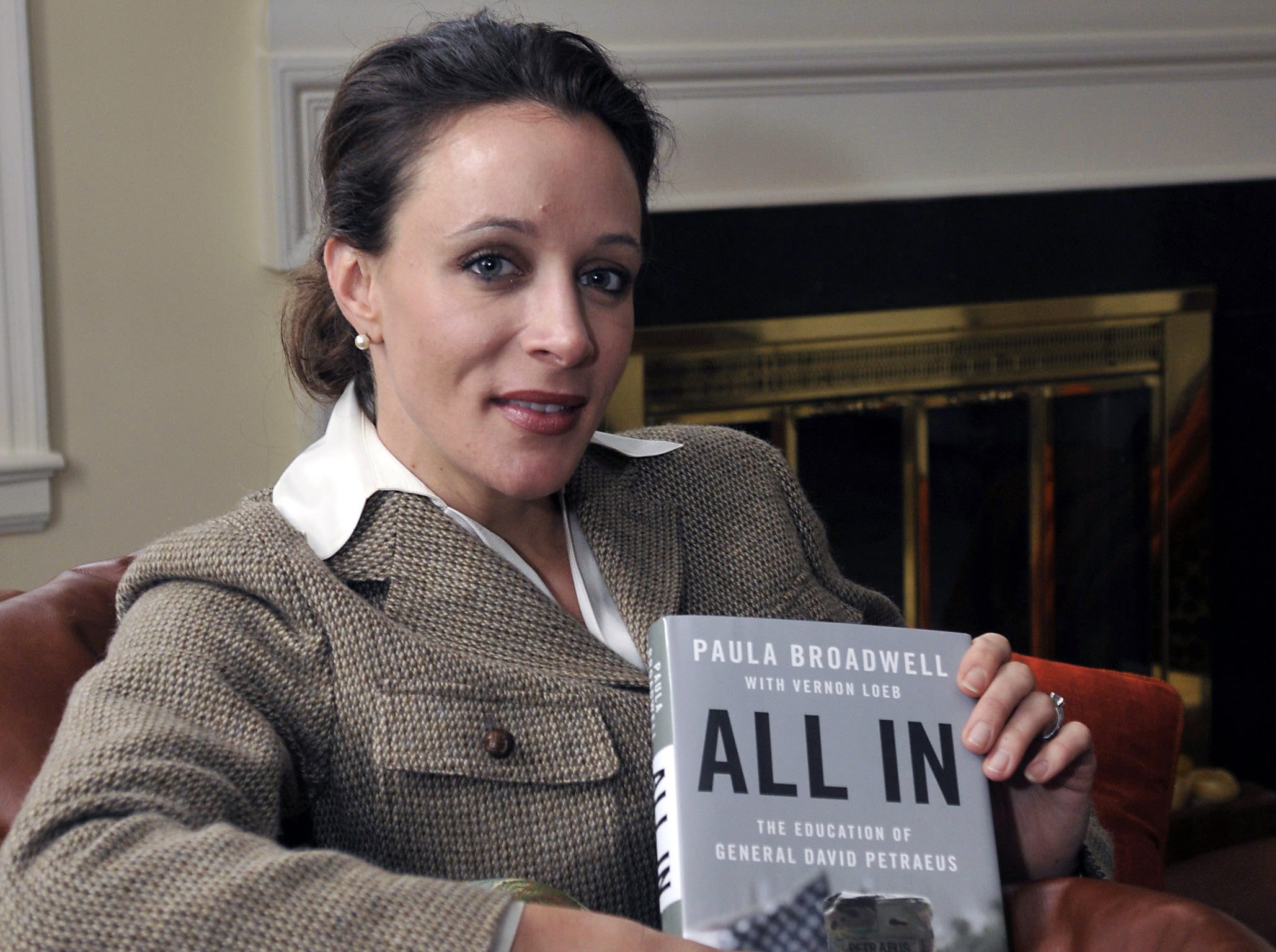
When none of those paths bore results, investigators settled on the single target they are scrutinizing now: Paula Broadwell, the retired general's biographer and mistress, and what she was doing with a cache of classified but apparently inconsequential files.
On Capitol Hill, the case has drawn references to the era of J. Edgar Hoover, the founding director of the FBI, who was notorious for digging up dirt on Washington's elite long before the invention of e-mail and the Internet.
"The expansive data that is available electronically now means that when you're looking for one thing, the chances of finding a whole host of other things is exponentially greater," said Rep. Adam Schiff, D-Calif., a member of the House intelligence committee and a former federal prosecutor.
In this case, Schiff said, the probe may have caused more harm than it uncovered. "It's very possible that the most significant damage done to national security was the loss of General Petraeus himself," Schiff said.
The investigation's profile has called attention to what legal and privacy experts say are the difficulties of applying constraints meant for gathering physical evidence to online detective work.
Law enforcement officers conducting a legal search have always been able to pursue evidence of other crimes sitting in "plain view." Investigators with a warrant to search a house for drugs can seize evidence of another crime, such as bombmaking. But the warrant does not allow them to barge into the house next door.
But what are the comparable boundaries online? Does a warrant to search an e-mail account expose the communications of anyone who exchanged messages with the target?
Similarly, FBI agents monitoring wiretaps have always been obligated to put down their headphones when the conversation is clearly not about a criminal enterprise. It's known as minimization, a process followed by intelligence and law enforcement agencies to protect the privacy of innocent people.
"It's harder to do with e-mails, because unlike a phone, you can't just turn it off once you figure out the conversation didn't relate to what you're investigating," said Michael DuBose, a former chief of the Justice Department's Computer Crime and Intellectual Property Section who now handles cyber investigations for Kroll Advisory Solutions.
Some federal prosecutors have sought to establish a "wall" whereby one set of agents conducts a first review of material, disclosing to the investigating agents only what is relevant. But Michael Sussmann, a former federal prosecutor who consults on electronic surveillance issues, said he thinks "that's the exception rather than the rule."
It's unclear whether the FBI made any attempt to minimize its intrusion into the e-mails exchanged by Broadwell and Petraeus, both of whom are married, that provided a gaping view into their adulterous relationship.
Many details surrounding the case remain unclear. The FBI declined to respond to a list of questions submitted by The Washington Post on its handling of personal information in the course of the Petraeus investigation. The bureau also declined to discuss even the broad guidelines for safeguarding the privacy of ordinary citizens whose e-mails might surface in similarly inadvertent fashion.
The scope of the issue is considerable, because the exploding use of e-mail has created a new and potent investigative resource for the FBI and other law enforcement agencies. Law enforcement demands for e-mail and other electronic communications from providers such as Google, Comcast and Yahoo are now so routine that the companies employ teams of analysts to sort through thousands of requests a month. Very few are turned down.
Although the Petraeus-Broadwell investigation ensnared high-ranking officials and had potential national security implications, the way the FBI assembled evidence in the case was not extraordinary, according to several experts.
The probe was triggered when a Florida socialite with ties to Petraeus and Gen. John Allen, the U.S. military commander in Afghanistan, went to the FBI in June with menacing e-mails from an anonymous sender.
Schiff and others have questioned why the FBI even initiated the case. Law enforcement officials have explained that they were concerned because the earliest e-mails indicated that the sender had access to details of the personal schedules of Petraeus and Allen.
The FBI's first pile of data came from Jill Kelley, who got to know Petraeus and Allen when she worked as an unofficial social liaison at the military base in Tampa, Fla. where both men were assigned.
Early last summer, Kelley received several anonymous e-mails warning her to stay away from Allen and Petraeus. Kelley was alarmed and turned over her computer to the FBI; she may also have allowed access to her e-mail accounts.
The e-mails were eventually traced to Broadwell, who thought that Kelley was a threat to her relationship with Petraeus, law enforcement officials said. But the trail to Broadwell was convoluted.
Broadwell reportedly tried to cover her tracks by using as many as four anonymous e-mail accounts and sending the messages from computers in business centers at hotels where she was staying while on a nationwide tour promoting her biography of Petraeus. According to some accounts, the FBI traced the e-mails to those hotels, then examined registries for names of guests who were checked in at the time.
Once Broadwell was identified, FBI agents would have gone to Internet service providers with warrants for access to her accounts. Experts said companies typically comply by sending discs that contain a sender's entire collection of accounts, enabling the FBI to search the inbox, draft messages and even deleted correspondence not yet fully erased.
"You're asking them for e-mails relevant to the investigation, but as a practical matter, they let you look at everything," said a former federal prosecutor who, like many interviewed for this article, spoke on the condition on anonymity because the FBI inquiry is continuing.
FBI agents can then roam through every corner of the account as if it were their own.
The capability to scour e-mail accounts has expanded the bureau's investigative power dramatically, even in crimes previously seen as difficult to prosecute. For example, officials said, the ability to reconstruct communications between reporters and their sources helps explain why the Obama administration has been able to bring more leak prosecutions than all of its predecessors combined.
E-mail searches vary in scope and technique, from scanning contents for key words "to literally going through and opening every file and looking at what it says," a former Justice Department official said.
Law enforcement officials said the FBI never sought access to Allen's computer or accounts. It's unclear whether it did so with Petraeus. But through Kelley and Broadwell, the bureau had amassed an enormous amount of data on the two men — including sexually explicit e-mails between Petraeus and Broadwell and questionable communications between Allen and Kelley.
Petraeus and Broadwell had tried to conceal their communications by typing drafts of messages, hitting "save" but not "send," and then sharing passwords that provided access to the drafts. But experts said that ruse would have posed no obstacle for the FBI, since agents had full access to the e-mail accounts.
As they pore over data, FBI agents are not supposed to search for key words unrelated to the warrant under which the data were obtained. But if they are simply reading through document after document, they can pursue new leads that surface.
"Most times, if you found evidence of a second crime, you would stop and go back and get a second warrant" to avoid a courtroom fight over admissibility of evidence, a former prosecutor said. But in practical terms, there is no limit on the number of investigations that access to an e-mail account may spawn.
There is nothing illegal about the Petraeus-Broadwell affair under federal law. Were it not for Petraeus' prominent position, the probe might have ended with no consequence. But because of his job — and the concern that intelligence officers caught in compromising positions could be susceptible to blackmail — the probe wasn't shut down.
"If this had all started involving someone who was not the director of the CIA . . . they would have ignored it," said David Sobel, senior counsel for the Electronic Frontier Foundation, a privacy group. "A bell went off because of who it was."
That consideration triggered a cascade of additional quandaries for the Justice Department, including whether and when to notify Congress and the White House. The FBI finally did so on election night, Nov. 6, when Deputy Director Sean Joyce called Petraeus's boss, Director of National Intelligence James Clapper Jr.
After being confronted by Clapper, Petraeus agreed to resign.
President Barack Obama said last week that there was "no evidence at this point, from what I've seen, that classified information was disclosed that in any way would have had a negative impact on our national security."
But the data assembled on Allen and Petraeus continue to reverberate. The FBI turned over its stockpile of material on Allen — said to contain as many as 30,000 pages of e-mail transcripts — to the Defense Department, prompting the Pentagon inspector general to start an investigation.
The CIA has also launched an inspector general investigation into Petraeus and his 14-month tenure at the agency, seeking to determine, among other things, whether he used the perks of the position to enable his affair with Broadwell.
If it follows its own protocols, the FBI will hold on to the data for decades. Former officials said the bureau retains records for 20 years for closed criminal investigations, and 30 years for closed national security probes.
- - -
Sari Horwitz and Julie Tate contributed to this report.
Join our commenting forum
Join thought-provoking conversations, follow other Independent readers and see their replies
Comments
Bookmark popover
Removed from bookmarks