Spy ties and Coke bottle cameras: Inside the Bulgarian gang’s James Bond-style spyware
Over the course of three years, five Bulgarian individuals, assisted by a host of others, carried out sophisticated surveillance on British soil and fed secrets back to their Russian handler, writes Holly Evans


Using spy ties, cameras hidden inside Coke bottles and over 200 mobile phones, a UK-based espionage ring would soon emerge as the “largest spying investigation” for counter-terrorism in the UK.
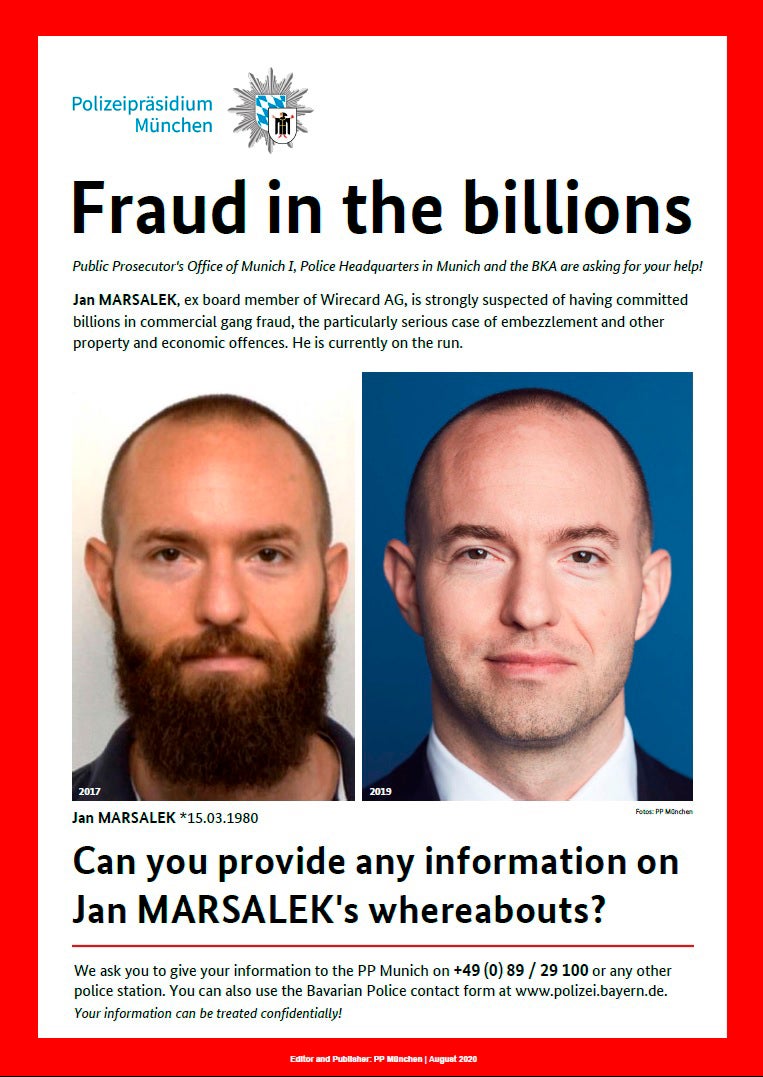
Over the course of three years, five Bulgarian individuals, assisted by a host of others, carried out sophisticated surveillance on British soil and fed secrets back to their Russian handler, former Wirecard chief operating officer Jan Marsalek.
Describing the scale of the investigation as “unbelievable”, the Met Police said the group had accumulated 33 audio devices, 55 visual recording devices, 221 mobile phone phones, 495 SIM cards, 11 drones, 75 passports and 91 bank cards in various names.
But perhaps even more fascinating was the incredible array of spyware this seemingly unassuming group had access to.
A false rock containing a camera, transmitters, surveillance devices hidden within a pen, adapted watches and two spy ties were among the advanced spy gear was also found during a raid at the Great Yarmouth home of Orlin Roussev, one of the group’s two ringleaders.

Little is known about the defendants’ backgrounds, apart from the fact that Roussev was “highly technically skilled” and had mastered forging fake ID documents and hacking devices.
He had even bragged in his messages to Marsalek that he was becoming like the James Bond character “Q”, and described his room of spygear as his “Indiana Jones warehouse”.
He appeared startled when police officers in balaclavas barged into his rooms and initially claimed they had got the “wrong place”, before relenting once they showed a search warrant.
Due to the vast amount of spyware in the former guesthouse, it took more than a week to search the property and nearly 2,000 exhibits were seized.
Counter-terrorism commander Dominic Murphy said some of the items were “things you definitely read about in spy novels – like a hidden rock spy”.
Among the gadgets, officers found a Minion toy with a camera hidden inside a fabric flower, as well as a picture and video of one of the women wearing the spy glasses. Remarkably, the second woman involved in the spy ring had been able to follow target Roman Dobrokhotov onboard a flight, filming him with a secret camera inside her shoulder strap and sending live updates to a group chat.
These updates included that he had two phones, used social media, listened to music, played Sodoku, and his pin for his mobile phone.

Noting this showed the “severity of the threat”, Commander Murphy, head of the Met Police’s Counter Terrorism Command unit, said: “They talked about how they were able to gain access to confidential flight data to sit near a journalist, using a camera to obtain his phone pin.
“The lengths they were willing to go to in this case were extreme. We never disregard the threat of Russia, many of our other jobs in this area relate to the threat posed by Russia.”
The remarkable extent of the spyware can be revealed after Katrin Ivanova, 33, Vanya Gaberova, 30, and Tihomir Ivanov Ivanchev, 39, were all found guilty following an Old Bailey trial, while the group’s two ringleaders, Roussev and Biser Dzhambazov, had already admitted their role.
Commander Murphy described it as “probably the largest spying investigation I’m aware of and have been involved in over 20 years of counterterrorism”.
“It was spying on an almost industrial scale on behalf of the Russian state and Russian intelligence, it goes to the heart of freedom and national security.”
“This group really were a serious threat and when they might have approached it quite lighthearted, they were carrying out sophisticated surveillance operations,” he added.
Commander Murphy said it was a “tangible example” of the current threat facing the UK, with Russian intelligence services increasingly turning to criminal proxy groups already based in the country, rather than utilising their own agents.
Between 2020 and 2023, the group orchestrated six plots targeting Russian dissidents, investigative journalists and a Kazakhstani politician, as well as undertook surveillance on a US airbase in Germany which trained Ukrainian soldiers.
Threats posed by states such as Russia and Iran now amount to 20 per cent of counter terrorism’s workload, with the Met Police noting a change in the way Russian intelligence operate by outsourcing their activities.
Their handler, Marsalek, has been on the run since June 2020 and is wanted by Interpol and the German police after $2bn went missing from the financial services provider Wirecard. After fleeing Germany, he is believed to be hiding in Moscow and has been involved with Russian intelligence since at least 2014.

Prosecutor Alison Morgan KC said there were six spying operations which involved “high level espionage with high levels of deceit” which were “extremely risky” for those involved.
They included getting close to their targets, filming them, and even envisaging direct contact by deploying the female defendants as a “honey trap”, as sexual bail to capture more information, jurors heard.
The first operation, between September and November 2021, targeted Bellingcat investigative journalist Christo Grozev whose work on Russian affairs included uncovering Russian links to the 2018 Salisbury attack and the downing of a Malaysia Airlines plane in July 2014.
The second operation in November 2022 focused on UK-based Russian dissident Mr Dobrokhotov.
Jurors heard he is an investigative journalist and founder of The Insider, a media organisation which was formerly based in Russia before he fled the country.
The third operation was on Kazakhstan former politician Bergey Ryskaliyev who fled to the UK and was granted refugee status.
The targeting of the political dissident in November 2021 would have helped cultivate relations between Russia and Kazakhstan, it was claimed.
The fourth operation involved staging a fake demonstration outside the Kazakh Embassy in September 2022 to create a pretence the spies had genuine intelligence about those responsible to pass on to Kazakhstan Intelligence Services to further curry favour, jurors heard.
This operation was conducted with a man called Ivan Stoyanov, jurors were told.
The fifth operation concerned Patch Barracks, a US military airbase in Stuttgart, Germany, in 2022, where Ukrainian soldiers were believed to be trained.
Ms Morgan said the defendants were using “highly sophisticated technology” to gather sensitive intelligence from the base.
The sixth operation targeted Russian lawyer Kirill Kachur when he was spending time in Montenegro between September 2021 and January 2022.
